Cloud-proxied ZTNA routes ITAR and CUI data through third-party infrastructure, expanding your compliance boundary. Sovereign ZTNA keeps data on your network. This guide covers ITAR, CMMC 2.0, FedRAMP requirements and how direct-routed ZTNA maps to specific controls.
Blog
Coffee shop networking says treat every network as untrusted and move the intelligence to an overlay. The idea is sound, but IP address conflicts, unreliable transport, and M&A make it harder than it sounds. Here's how Bowtie solves the hard parts.
Trust in vendors to prioritize customer security over their own success is misplaced. Creating expensive, incompatible duplicates of popular products for ‘discerning’ customers discredits the vendor’s security commitment to its broader customer base and balkanizes feature sets.
Bowtie introduces HTTPS WebSocket tunneling to ensure robust, compliant, and discreet network connectivity – no matter how restrictive your operating environment.
VPNs grant network-level access and create the conditions for lateral movement. ZTNA replaces them with application-level access, continuous verification, and per-session authorization. Here is the architectural difference, the cost comparison, and how to migrate.
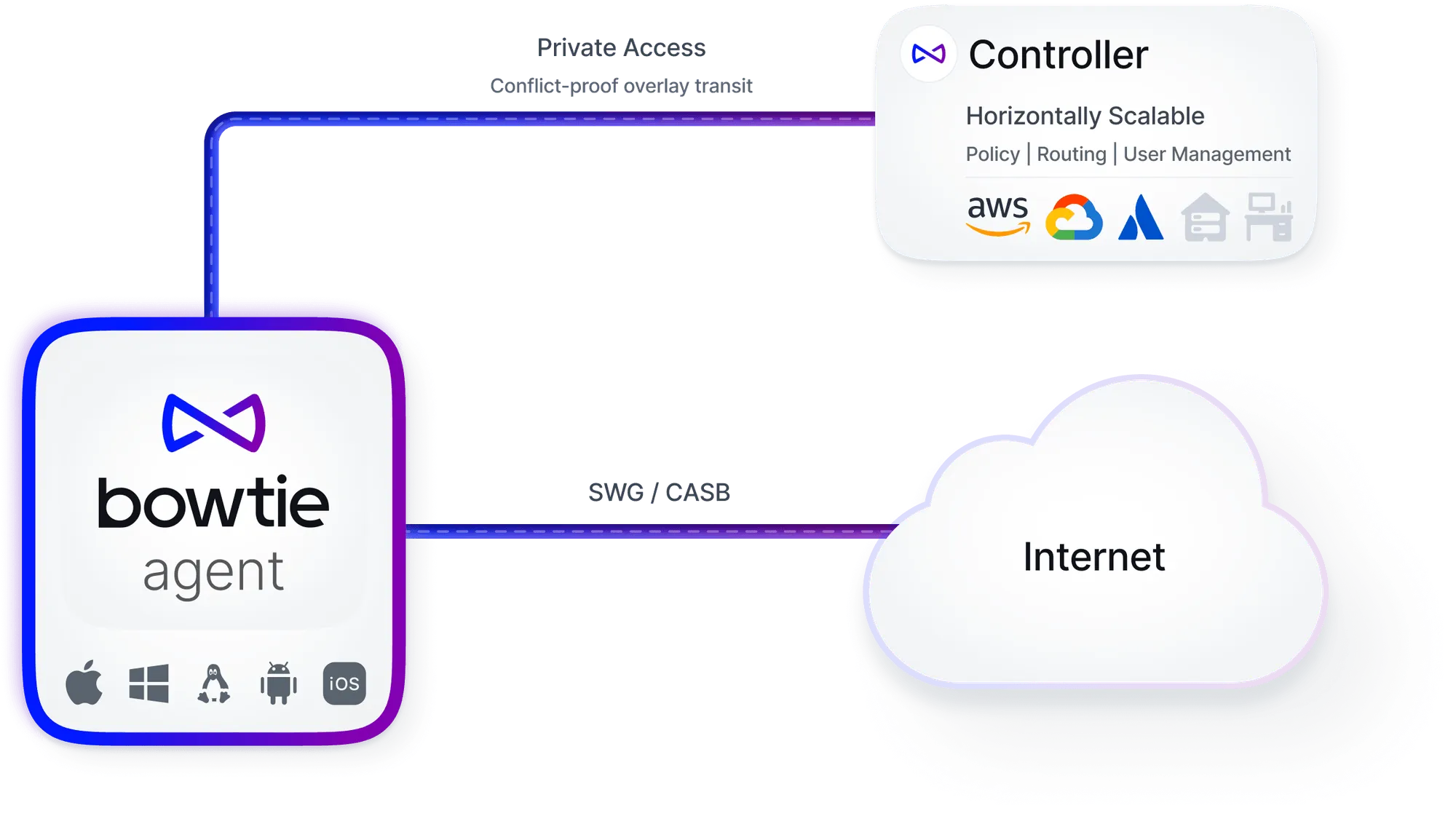
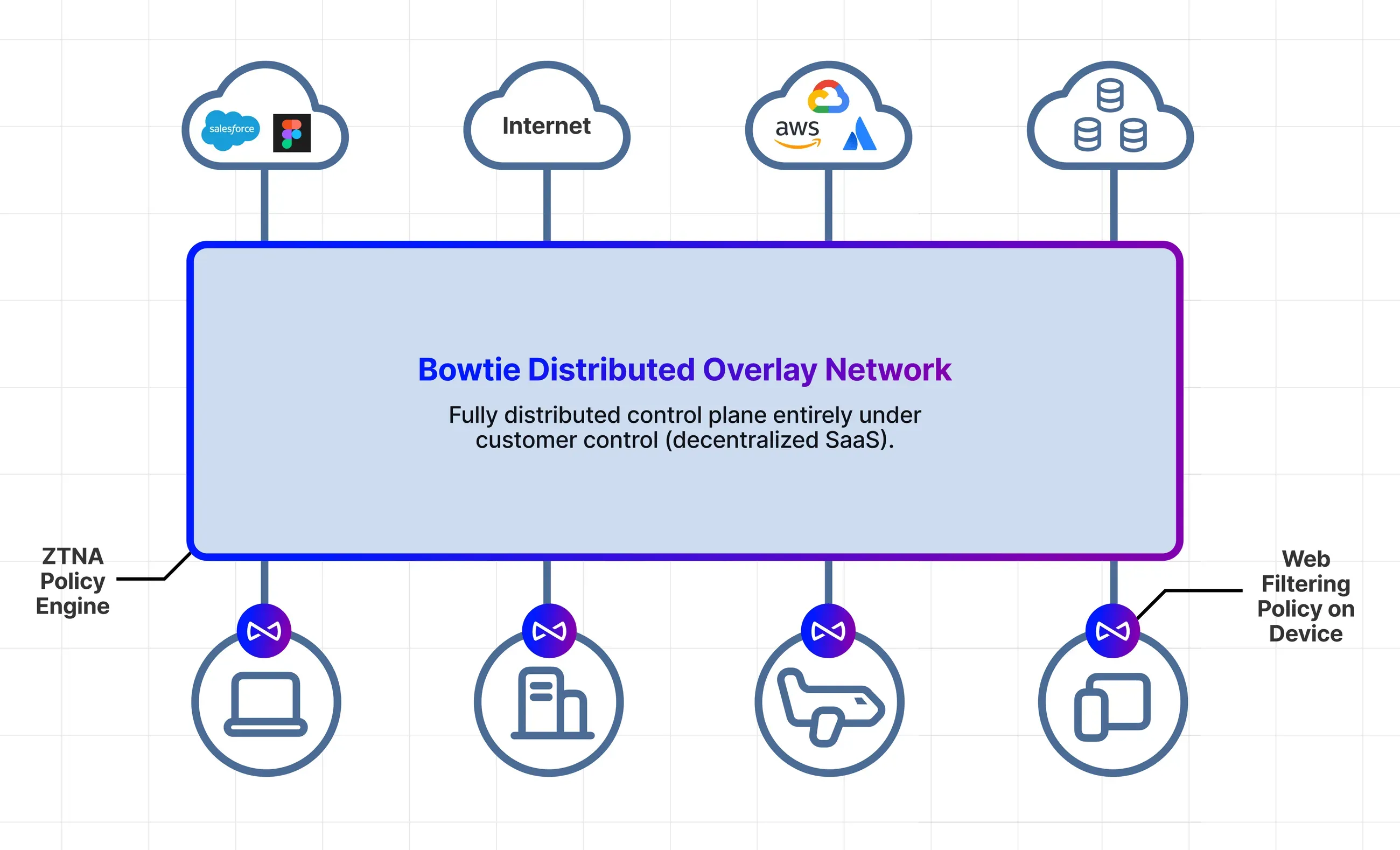
A technical comparison of Bowtie and Zscaler architectures. Bowtie keeps data on your infrastructure. Zscaler routes everything through their cloud. This post covers data flow differences, compliance implications, and pricing.
Fast Flux is a DNS-based evasion tactic that breaks IP blocklists. We unpack how attackers use it to stay ahead and why conventional SASE tools can’t keep up — then show how Bowtie neutralizes Fast Flux with DNS-layer enforcement and decentralized control.
Sovereign SASE keeps your data off third-party clouds while delivering the same security functions as cloud-delivered SASE. This post explains the architecture, deployment model, and why it matters for regulated industries.
The Digital Operational Resilience Act (DORA) requires EU financial institutions to strengthen IT resilience by January 2025. This guide covers what DORA means for network security architecture and how zero trust helps meet requirements.
Zero Trust Network Access (ZTNA) replaces VPN-style network access with application-level controls. No implicit trust, continuous verification, and no lateral movement. This guide covers the architecture, components, benefits, and implementation challenges.
A look at how Bowtie's unique architecture and design helps make network conflicts, network sprawl, and challenges associated with RFC 1918 a thing of the past.
Bowtie's innovative architecture empowers businesses to access private resources without being in the middle of the process. This detailed post is the first in a series on our control plane, first delving into our use of Automerge—a 'Local First' conflict-free data type implementation. Discover how Bowtie achieves resilient, scalable, and partition-tolerant networking, facilitating seamless and efficient integration across multiple sites.
SASE combines network security and wide-area networking into a single cloud-delivered service. This guide covers the architecture, how SASE relates to ZTNA, and why data sovereignty matters when choosing a SASE provider.
The industry is hurtling towards the SaaSification of everything, but what does this mean for customers and vendors alike? This in-depth post explores the complex landscape of SaaS, highlighting both its promises and costs, especially in areas like security and autonomy. Through real examples and historical security failures, we suggest a more critical approach to embracing the SaaS model.
Learn how Bowtie uses Nix to build network appliance images, enabling us to support a variety of formats with a high degree of code reuse and an elegant upgrade process. Ensuring that network appliances are easy to run, test, update, and operate reliably is important and underpins Bowtie’s commitment to robust simplicity.
There is a better way to build enterprise networks. Bowtie is building for this future. The network is everywhere now.
The who, what, and why of Bowtie. Mostly the why.
Built for CISOs.
Loved by engineers.
Trusted by Ops
Ready to unify and harden your missions stack?
















.avif)